Mitigating Risk with Human-in-the-Loop AI Systems
How the Hold Protocol prevents unauthorized payload egress and enforces Command & Control (C2) without sacrificing operational velocity.
Actionable research at the intersection of data science, operational reality, and military-grade discipline. We publish the exact frameworks we use to build autonomous systems.

The tech industry sells tools. We build systems. An exploration of why the "bolt-on" approach to artificial intelligence fundamentally fails the modern enterprise, and how to transition to a systems-first architecture.
Read Briefing
How the Hold Protocol prevents unauthorized payload egress and enforces Command & Control (C2) without sacrificing operational velocity.
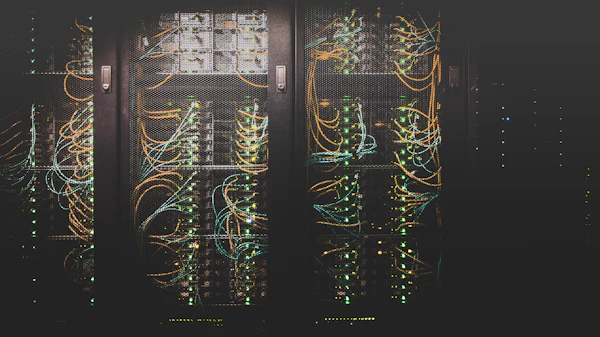
An AI agent is only as intelligent as the data it accesses. A technical roadmap for untangling legacy on-premise databases for RAG integration.

A breakdown of exactly where field service organizations are bleeding margin to manual data entry, and how voice-to-CRM pipelines solve it.
A definitive 44-page guide to scaling Enterprise AI, embedding governance, and securing the operational perimeter. Designed for executive leadership.
Download the Playbook